Featured Image: Carey Seay | Marlin Chronicle
Aside from homework, tests, projects and extracurricular activities, Microsoft Authenticator can make doing basic tasks on Blackboard seem like jumping through hoops. The new two-step verification for Microsoft Authenticator requires students and faculty members to have the Microsoft Authenticator app on their mobile devices. This has proven difficult for some people for a multitude of reasons, while others don’t necessarily mind the two-step authentication process.
The Microsoft Authenticator app is a safe and secure way to protect Microsoft accounts and information. This type of secure login is used by many schools and companies to ensure the security of the accounts of their users.
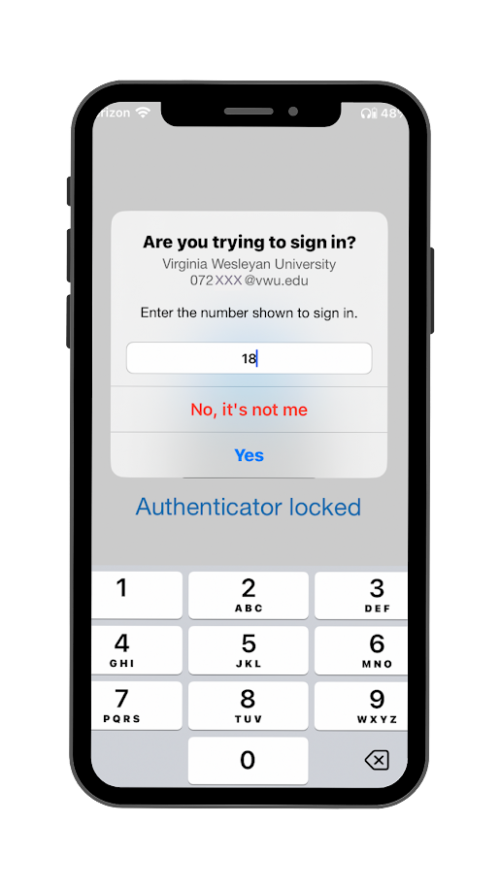
Now that Microsoft Authenticator is slowly doing away with text message verification, the app used for two-step authentication is becoming a must-have. The dual authentication process is designed to be incredibly simple. With the app on a mobile device, students and faculty members can simply type in a provided code to access their accounts.
The two-step authentication is advertised as more secure than simply typing in a password. As one would expect, this gives the sign in process a second wall of security. The Microsoft support website said, “Two-step verification helps protect you by making it more difficult for someone else to sign in to your Microsoft account. It uses two different forms of identity: your password, and a contact method.”
This simple way of confirming the identity of the person attempting to sign in to the account is incredibly beneficial and gives many people peace of mind.
First-year Gabrielle Barnett says she likes the extra security this dual authentication process provides.
“I don’t have to worry about people breaking into my school account,” Barnett said. “Since I have a lot of private information on there, and I feel like my passwords are relatively easy to guess, I like that.”
Occasionally, students and faculty members have experienced situations where they can’t use the Microsoft Authentication app.
Junior Kaitlyn Duswalt was without a phone for two weeks when she broke it earlier this fall. Luckily, Duswalt had already opted to have her accounts automatically authenticated for seven days. After the first seven days, however, Duswalt had to do something to be able to access her accounts.
There was a relatively easy solution, thankfully. Duswalt simply had to contact the Malbon Center for Technology to explain the situation. The solution from there was to have Duswalt’s authentication account transferred to her boyfriend’s phone temporarily.
This, of course, proved to be inconvenient when the two were separate during the day and Duswalt needed the code for authentication. Duswalt would have to email her boyfriend when she needed the code for authentication, which wasn’t the most reliable form of communication.
Duswalt said the entire process was easy enough, but it was ultimately “kind of annoying. I wouldn’t recommend it.”
Dr. Stephen Hock, associate professor of English, has a different problem when it comes to using Microsoft Authenticator. Hock does not own a mobile phone and, therefore, is unable to use the Microsoft Authenticator app to complete the two-step authentication process.
Hock has two ways of successfully using the two-step authentication. One method is to have the Microsoft Authenticator programmed to call a landline. This is useful only when there is access to a landline. For when there is no landline, another method must be used.
For this type of situation, Hock has a small USB flash drive, provided by the Malbon Center for Technology, that acts as a key to the Microsoft Authenticator. It’s as simple as plugging the drive into a computer and entering a security code.
Since beginning to use these methods last year, Hock has not encountered any major problems to make the process inconvenient. Even in situations that are not generally taken into account by large corporations, such as Microsoft, there are some solutions available for problems that may arise.
While the dual authentication process may seem like an inconvenience to many students and faculty members, even without having to jump through hurdles, Hock said, “It’s becoming the standard wherever you work.”
This is certainly becoming more and more relevant as new technology is replacing the innovations of the past. Students and faculty alike should also remember that the dual authentication, while annoying, is there for the protection of personal information and to guard against major problems like hackers.
By Calee Lukowski